Today’s global maritime sector is increasingly dependent on digitization, operational integration, and automation. The widespread and rapid implementation of IT systems and internet communications for ships at sea in all parts of the world carries with it a new and urgent obligation – maintaining the operational safety of these vital systems.
Cyber security is a priority in the international maritime sector today. In this blog, we will take a close look at the new requirements that we all now must meet and focus on the guidance for implementing cybersecurity in the maritime sector.
In the past, neither the International Maritime Organization (IMO) nor the national authorities had developed specific cybersecurity regulations for the maritime sector. This changed from January 1, 2021, as the cybersecurity requirements were formalized in Chapter IX of the International Convention for the Safety of Life at Sea SOLAS, Regulations 1-6, Management for the Safe Operation of Ships.
The IMO’s Resolution MSC.428(98) encourages administrations to ensure that cyber risks are appropriately addressed in existing safety management systems (as defined in the ISM Code) no later than the first annual verification of the company’s Document of Compliance (DOC) after 1 January 2021.
This is not an isolated development. Substantial steps towards cybersecurity regulations for shipping have already been taken by other organizations or are in preparation. Indeed, the urgent need to develop cybersecurity regulations for the maritime industry has been a cause for concern for some time.
In June 2017, the IMO’s Maritime Safety Committee, MSC, agreed on guidelines for cyber risk management. These in turn formed the basis for high-level recommendations for the entire maritime sector. The guidelines oblige shipowners, operators, and stakeholders to adopt a risk management approach with three overarching goals: minimizing the dangers for the crew, for environmental safety, and the financial consequences of a complete or partial loss of the availability, integrity, and confidentiality of sensitive data.
The Present Picture
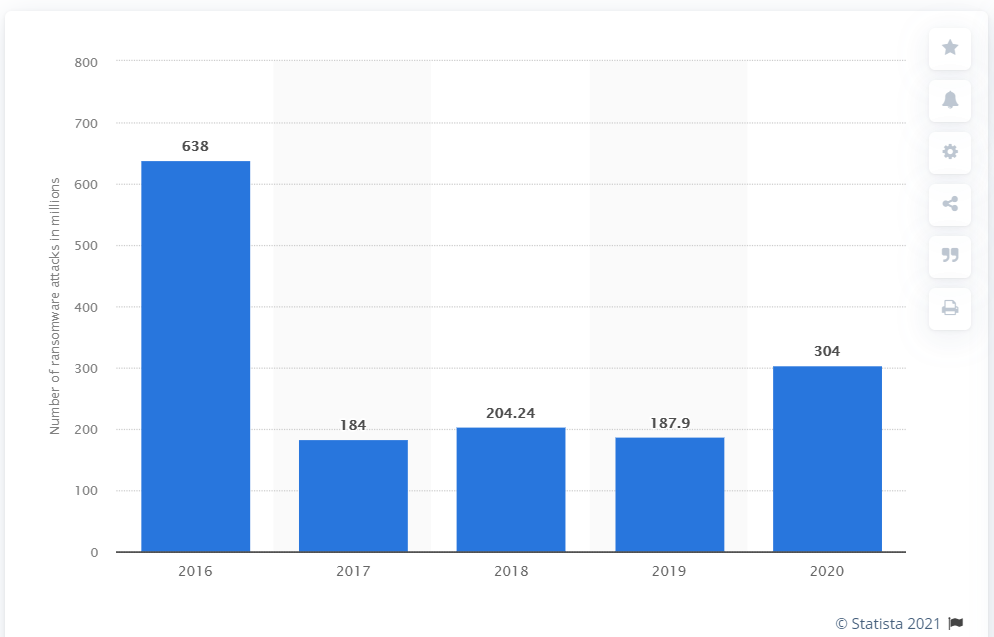
The move to digitize shipping means greater reliance on digital and communication systems, which leaves more room for a potential cyber security incident. Recent events in the maritime industry have shown that cyber threats are becoming a reality. As per reports from Splash247, the number of shipping cyber-attacks has leaped 400% since February 2020.
In Sept. 2020, the French shipping company CMA CGM announced it had been hit by a ransomware attack. The “Ragnar Locker ransomware” attacked Chinese branches in Guangzhou, Shenzhen, and Shanghai and took down its worldwide shipping container booking system.
This recent attack marks a unique scenario because CMA CGM is now the 4th major shipping company to be hit by a cyber-attack in the past four years. In fact, according to ZDNet, “there is no other industry sector where the Big Four have suffered major cyber-attacks one after the other like this.”
Previous incidents with the “Big Four” since 2017 include:
- APM-Maersk– taken down for multiple weeks by Not Petya ransomware in 2017
- Mediterranean Shipping Company– attacked in April 2020 by an unnamed malware strain that brought its data center down for days.
- COSCO – In July 2018, it was brought down for weeks due to ransomware.
While all four of these incidents are different, they do show that there is a targeting of the maritime shipping industry.
And the attacks do not stop there!
Over the past year, incidents where malware landing on ships has grown, including sightings of USB malware, ransomware, and worms that have been found aboard a ship’s IT systems.

Attacks have not just been involved with targeting ships. In a statement on Thursday, Oct. 2, the International Maritime Organization (IMO) said it suffered “a sophisticated cyber-attack against the organization’s IT systems.” The attack caused several IMO web-based services to be unavailable and the breach also impacted its public website and internal systems.
Although it might be too soon to say whether the recent attacks will prove to be a brief annoyance or the start of wider damage, Bloomberg Intelligence’s Lee Klaskow says the cyber threats are a “near-term headwind and headache for sure.”
Future Expectation
“We thought we were prepared for a cyber-attack and then we got a nasty surprise when one actually occurred.” This is a common reaction of those who have lived through a cyber-attack.
An effective approach to cyber risk management actually starts with leadership. The latest IMO guidelines and the guidelines on cybersecurity on board ships (Version 3 of BIMCO et al.) Make it very clear that “effective cyber risk management should start at the top management level”.
How does your management team perceive cyber risk in shipping? Cyber risks must be owned and managed as a core business risk, with ultimate accountability at the executive level. If you, as an IT or HSSEQ manager, take on this perceived responsibility, it is in your best interest that your management team understands this.
What does a cyber-capable management team look like? The executive team needs to better understand the cyber risks the business faces, ensure that there is a sufficient budget to ensure cyber resilience, and set clear roles and responsibilities to maintain business continuity. This also includes knowing their role during a cyberattack crisis. Cyber drills offer a useful starting point here.
Ultimately, the goal here is to create increased awareness and understanding of cyber risks in your leadership team. It prepares them for when (and not if) a cyber-attack occurs. The exercise will also help you find ways to improve your company’s ability to implement effective mitigation strategies.
- How would they react?
- What information would they need to make decisions?
- Who do you need to communicate with and when?
We at Varuna Marine can help! Our fully managed cybersecurity solution comes with an owner dashboard that tracks all cybersecurity-related KPIs and always ensures compliance. Our team of cybersecurity experts conducts a soft and hard audit annually and every six months to ensure a complete test of readiness against external cyber-attacks.